2.4 KiB
| obj | website | repo |
|---|---|---|
| application | https://mitmproxy.org | https://github.com/mitmproxy/mitmproxy |
mitmproxy
mitmproxy is a set of tools that provide an interactive, SSL/TLS-capable intercepting proxy for HTTP/1, HTTP/2, and WebSockets.
Features
- Intercept HTTP & HTTPS requests and responses and modify them on the fly
- Save complete HTTP conversations for later replay and analysis
- Replay the client-side of an HTTP conversation
- Replay HTTP responses of a previously recorded server
- Reverse proxy mode to forward traffic to a specified server
- Transparent proxy mode on macOS and Linux
- Make scripted changes to HTTP traffic using Python
- SSL/TLS certificates for interception are generated on the fly
3 Powerful Core Tools
The mitmproxy project’s tools are a set of front-ends that expose common underlying functionality. When we talk about “mitmproxy” we usually refer to any of the three tools - they are just different front-ends to the same core proxy.
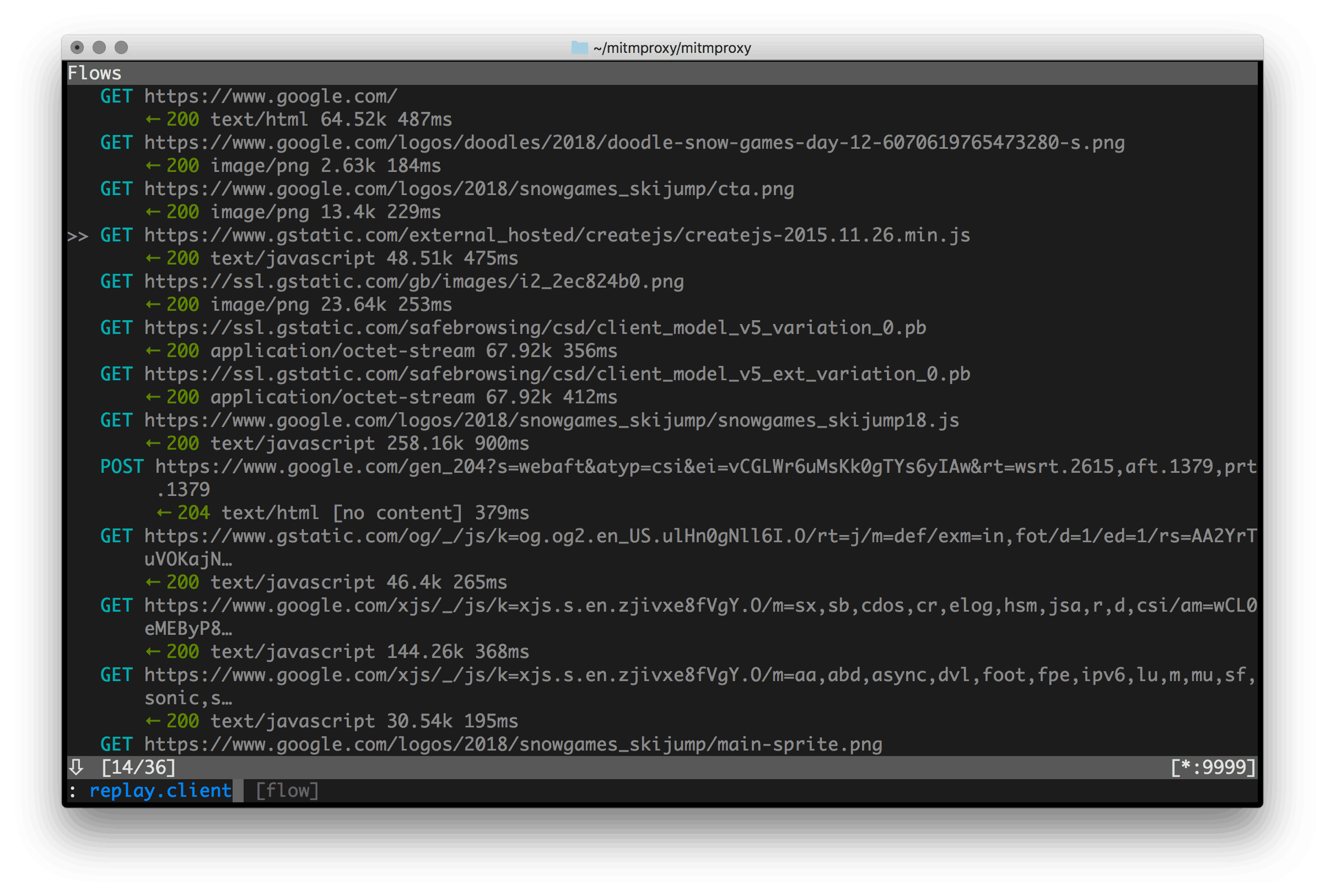
mitmproxy is an interactive, SSL/TLS-capable intercepting proxy with a console interface for HTTP/1, HTTP/2, and WebSockets.
mitmweb is a web-based interface for mitmproxy.
mitmdump is the command-line version of mitmproxy. Think tcpdump for HTTP.
Usage
Mitmproxy starts as a regular HTTP proxy by default and listens on http://localhost:8080.
You need to configure your browser or device to route all traffic through mitmproxy. Browser versions and configurations options frequently change, so we recommend to simply search the web on how to configure an HTTP proxy for your system. Some operating system have a global settings, some browser have their own, other applications use environment variables, etc.
You can check that your web traffic is going through mitmproxy by browsing to http://mitm.it - it should present you with a simple page to install the mitmproxy Certificate Authority - which is also the next step. Follow the instructions for your OS / system and install the CA.